Ensuring security with card-based access control systems
Overall, if an odd number of bits (including the parity bit) are transmitted incorrectly, the parity bit will be incorrect, thus indicating a parity error occurred in the transmission. The data must be discarded entirely and re-transmitted from scratch. In doing so, byte parity error detection helps provide extremely fast, accurate, and secure transmissions.
To operate:
- reader powers proximity card or tag;
- card transmits access data (e.g. facility code or ID number) to reader; and
- reader transmits access data to access controller via an industry standard protocol.
Now, smartcard technology will be reviewed. In operation, smartcard-readers typically generate an electromagnetic field tuned to 13.56 MHz. When a credential enters this field, the credential’s internal RFIC is activated. The RFIC then transmits its unique data back to the reader as an encoded modulated signal.
Smartcard-readers are typically able to read the sector (i.e. access control) data and/or unique card serial number (CSN) from ISO/ICE 14443-compliant smartcard credentials. Meeting the ISO standard, the cards are quite often programmed at the manufacturer with the brand’s compatible secure key. During the validation process, the credential’s secure key is challenged by the reader. If the secure keys match, the reader will read the card’s sector data; if the secure keys do not match, the reader may only read the credential’s CSN.
For example, to operate:
- reader and credential share and compare secure keys;
- keys match—the reader collects sector data (i.e. long beep); or
- keys do not match—the reader collects CSN (i.e. quick beep).
How can security be improved?
First of all, it should be noted these types of attacks are infrequent. However, with this in mind, there is a range of tools to negate skimming, eavesdropping, and relay attacks.

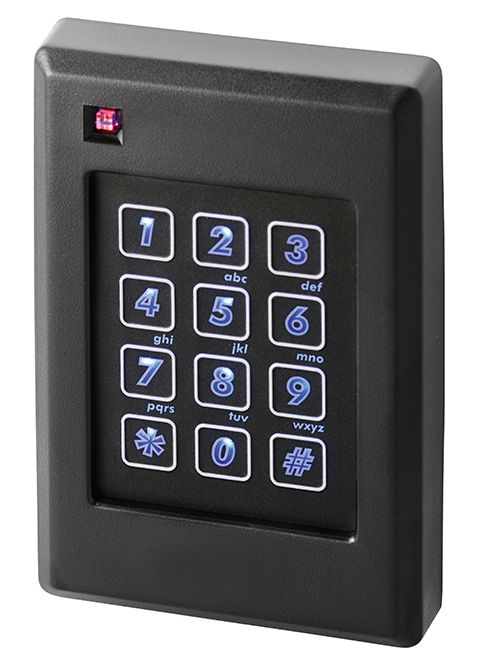
The security of proximity cards is increasing. One of the easiest solutions is to provide two-factor validation of the person wanting to enter. Not only must a person have something (e.g. authorized card or tag), but he or she must also know the personal identification number (PIN). Especially for those higher-security areas, a card-reader with an integrated keypad can be specified. To enter, the individual presents their card, gets a flash and beep, and then enters the PIN on the keypad. The electronic access control system then prompts a second beep on the reader, and the individual is authorized to enter.
Integrators can also provide a high-security ‘handshake,’ or code, between the card, tag, and reader to help prevent credential duplication and ensure customer’s readers will only collect data from specially coded credentials. In a sense, it is the electronic security equivalent of a mechanical key management system, in which a customer’s organization is the only one that has the key they use. Such keys are only available through the installing contractor, and another company is never provided with the same key.
In the electronic access control scenario, no other company will have the reader/card combination a customer can get from the building owner via the installer. Only its reader will be able to read their card or tag and their reader will read no other card or tag.
Smartcard systems, while often a cost comparable to proximity card systems, may be more secure and can be used for applications beyond access control, such as library checkouts or a hospital cafeteria.




